Basic Static and Dynamic Analysis – Report Writing
Although there are various malware finding as well as attack on applications, as well as to find we will first download infected Windows XP use MSRT (Malicious Software Removal Tool). The setback with the majority of anti-malware apparatus is all them require signatures to detect the malicious code in the Windows XP. At whatever time a latest virus, and any form of malware is revealed, the system requires to be updated, as on QUT virtual machine we will use anti-malware tools to find out the new-fangled malware. These malware are productive, although, as well as latest malware is revealed on an everyday base, as a result we have to use the MSRT like tools to find the malware in the windows. As is the case in this infected windows on QUT virtual machine, user are mostly left defenseless alongside the fresh fear for a number of sum of instance, which depends on how quickly the windows will be able to test as well as install updates for further verification of malware. This is the basis lots of windows users enclose the discernment with the intention of anti-malware tools won’t work well off. Frequently one tool might found out the malware which usually other misses, along with while a danger is relatively fresh, not many tools will be able to find it. As a result, the demand for malware clean-up technique shoots up. Even though to a great deal more expedient to immediately scamper an anti-malware appliance as well as expect for the utmost experience to complete the task. We can look into deeper for finding out manually as an alternative of coming up for the using any tool. We will be using the Sysinternals for the process of autorun and monitoring purpose.
Identify the Malware:
To manually detect malware we will do the following:
- Cut off our equipment from the network support.
- Recognize the malicious procedure as well as drivers.
- Postpone as well as stop the recognized procedure.
- Recognize as well as remove every malware auto set up.
- Remove the malware records.
- Reboot then replicate the steps.
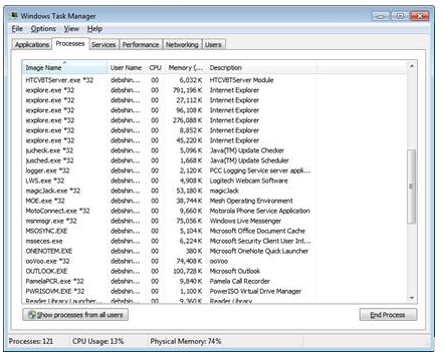
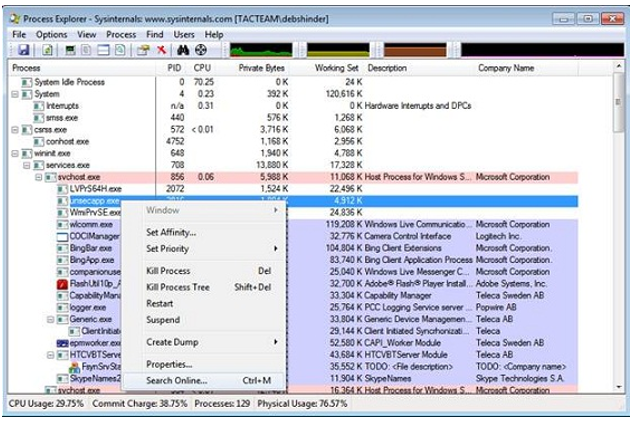
To find out the suspicious activities we will look for those procedures which icon have no evocative or business identification, or any undefined Microsoft imagery. In addition point out on those procedure which reside in the directory of windows, so as to include odd URLs in the unlock TCP/IP endpoints. A lot of are crammed – condensed or encrypted – as well as numerous malware will have their own packer signatures. The majority of malicious will have every one of this distinctiveness. As shown in the first figure we went to Windows to task manager.
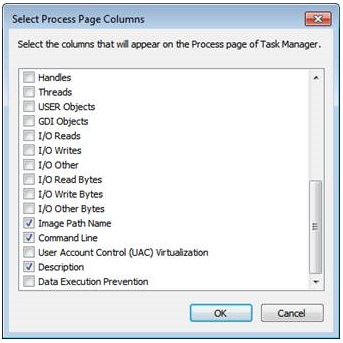
We should obtain extra data in Task Manager through View menu after that by clicking any Selected Columns, we will check the boxes according to user choice as shown below.
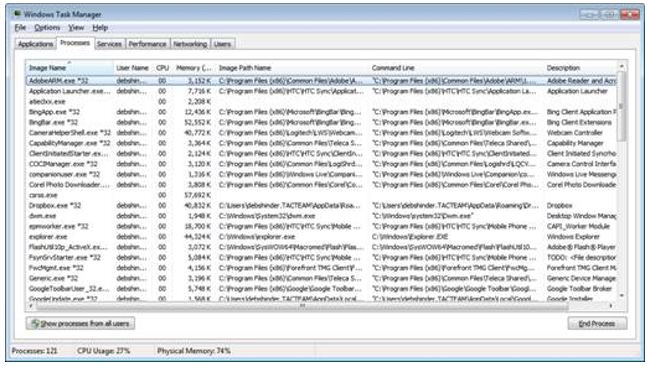
For instance, we have put on view the picture pathway name to demonstrate the complete pathway to the file which will be associated with the procedure. As shown in the image below for additional information.
After this we find out that Task Manager has not able to give us the in-depth glance for a processes so to get complete information we will use Sysinternals Process Explorer.
To Identify Malware Using Process Explorer
We will run this process explorer on infected windows xp which was downloaded from QUT virtual machine as shown in the image below, it offers us a diverse sight of the processes which will be done in the Task Manager.
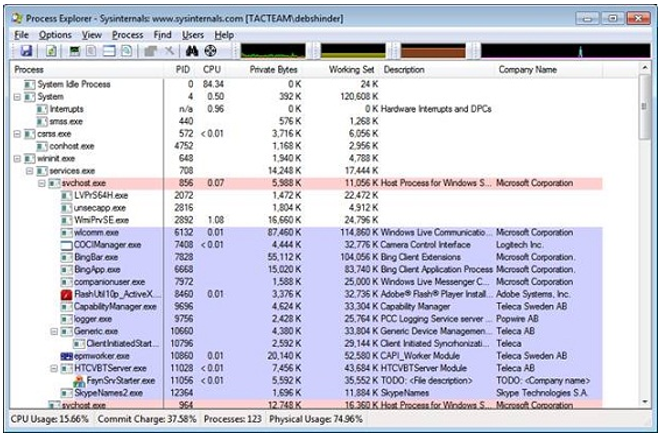
We will note that in Sysinternals Process Explorer, as shown the tree in the leftside column which will display parent-child associations. But whenever one process finds out to be doubtful, connected processes might in addition to be. An enormously helpful characteristic is the capability to right-click on process as well as select the “online Search” to get the information in relation to the process, see the image below.
One thing to remember is that few malware shall be utilized as pseudo arbitrary created controller names, keeping in mind the end goal to keep you from finding any data in a pursuit.
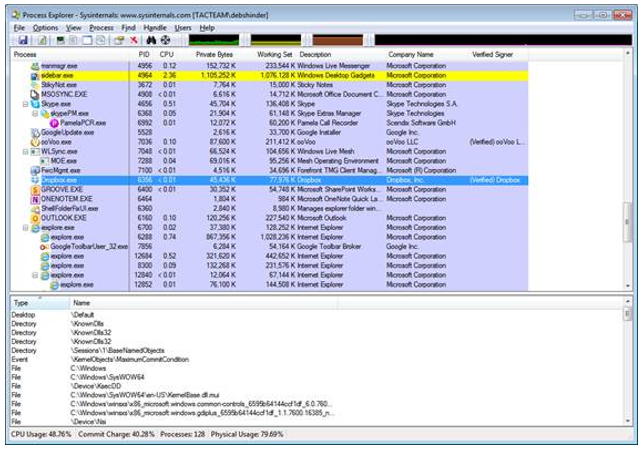
We noted before that malware is regularly pressed, in Process Explorer means that the records might be stuffed; Process Explorer searches for package heuristics to call over these procedures. While we take note of these procedures in Visual Studio repaired forms, they will always look like stuffed procedures. A part of these procedures shown might be exceptionally natural with the objective that we will not be giving them any idea about the procedures, for instance, taskhost.exe, rundll32 and svchost.exe, etcetera. In most of the cases, these malware essayists know this as well, as a result malware regularly take cover at the back of these procedures, who in particular make their own administration host to stow away in as well as keep running as framework procedures. The observation made by us forms guarantee that this window are not digitally marked, which is suspicious on the grounds that for all intents as well as purposes all Microsoft code has decided upon. We have specifically test out marks with the confirm catch on the procedure image tab, which shows in the Properties box for a procedure, and that can be accessed by double tapping on the procedure name. This can be seen in the below figure:

As soon as we have verified a process, this tool should join the Internet to verify the CRL (Certificate Revocation List). We should “Verified Signers” feature to this Sysinternals Process Explorer demonstration, on selection of View with selected Columns as well as examining the “Verified Signer” package as displayed below:

We can view in the image below the latest column along with the signatures which will be verified.
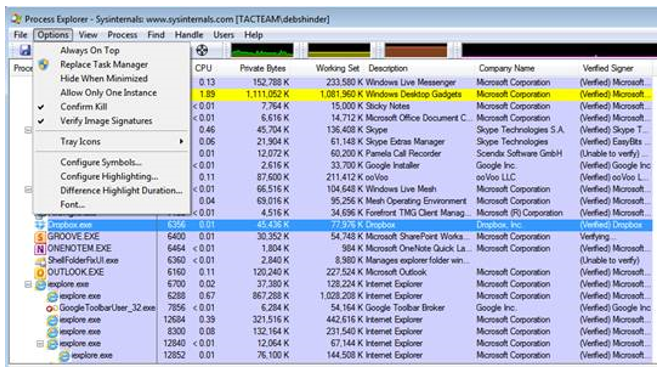
In case we want every signature to be verified, we should connect the option menu as well as choose “authenticate picture signatures” as displayed below.
Static Analysis
Once in a while we might wish to recognize what procedures are backing off from window xp, which generally implies we are contaminated with some sort of malware, for instance, infection, any Trojan virus. It is authentically straightforward to do as such utilize Windows XP Task Manager. Following are the ways to do it:
- In windows xp we use the keys CTRL+ALT+DELETEOr ESCAPE
- With a right-click an unfilled taskbar region as well as choose “Start Task Manager” from the Task bar
- On Key combination of CTRL+ALT+DELETE then choose “Start Task Manager”
On the off chance that none of these strategies conjure Windows Task Manager, it is probably due to this window x is tainted with malware plus requires extra techniques to end as well as evacuate the deadly disease in the system. As soon as it opens, choose “processes” label to view all at present running procedures on your PC. The window ought to resemble this:
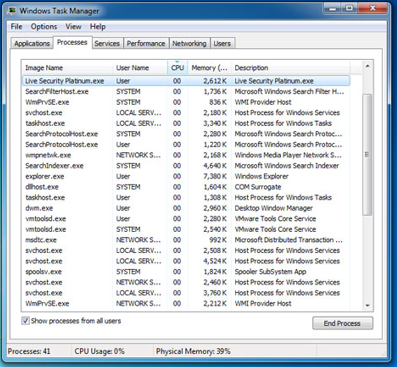
On the off chance that you need to discover which specific process is utilizing the vast majority of the system processor, tap on the “CPU” section to sort the rundown by CPU utilization. In this screenshot there is a vindictive procedure describe “Live Security Platinum.exe“. Noxious procedures more often than not either don’t have any depiction under “Portrayal” section. With a specific end goal to murder any suspicious procedure, right-tap on its name in Windows Task Manager as well as select “End Process” from the setting menu. Know that regardless of the possibility that the procedure is does not run anymore, pernicious records are as yet living on your PC’s hard drive and they will probably reactivate whenever you begin your PC. In this manner, you MUST evacuate all records identified with the contamination.
Dynamic Analysis
A vital piece of “knowing your system” is following endpoint diligence instruments and with the bunch of courses in Windows XP working framework can naturally stack as well as execute code. These foundation administrations have been a standout amongst the most generally used ingenuity areas in XP. This is accessible in view of the fact that the time of XP, these administrations give a solid approach to discretely stack procedures as well as figure out the sight upon framework client logon, boot, and activate the conditions. While, much consideration is frequently compensate to incognito tirelessness strategies, which is fundamental to not to send away the nuts as well as bolts out particularly given how pervasive administration based malware remains.
RATs (Remote Access Tools) as well as other malware will hold on the administrations in 3 distinctive routes: COM+ segments with remain solitary administration executables, facilitated assistance modules.
Remain Solitary Services
Remain solitary administrations run an executable record to summon line which will indicate the “ImagePath” with respect to exacting understanding registry keys. The Windows XP registry will contain the display settings for all solitary present administration which will show this parent input “HKLM\System|CurrentControlSet\Services“.
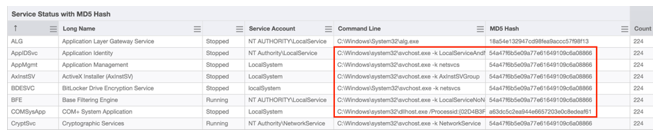
This “Administration Status with MD5 hash” sensor, for instance, gathers as well as look at the administration name, state, summon line, ImagePath hash, as well as the client setting under which the administration is running. This will imply that these remain solitary administrations which should emerge with a low recurrence of-event number if their arrangement or state is bizarre, or varies among indistinguishably named cases. These clients have used this sensor to recognize misconfigured yet authentic administrations in light of status, with maverick administrations on the premise of their client setting, name with contrasting ImagePath hashes for indistinctly named benefit occasions.
From an assailant point of view, remain solitary administrations are not as mainstream on the grounds that the executable way is promptly accessible utilizing these Task Manager. Consider an assailant which desires to mask malware under the true blue administration, “Print Spooler“. This administration has an executable way of “c:\windows\system32\spoolsv.exe“. This method can successfully conceal malware from initial examination, yet is effortlessly vanquished by factual stacking of the ImagePath.
Hosted Services as well as COM+ Applications
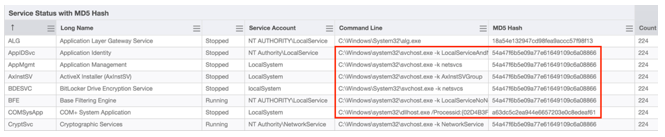
Facilitated administrations are actualized as libraries normally DLLs (Dynamic Link Libraries) as opposed to remain solitary executable documents. They are normally stacked by Windows XP benefit facilitating process, “svchost.exe“. The image beneath demonstrates the yield of “Administration Status with MD5 Hash” sensor for a few facilitated administrations, for instance, “Application Management” as well as “Base Filtering Engine“. For each administration, the offered hash is that of “svchost.exe” as an alternative of the facilitated DLL.
Facilitated benefit gatherings are arranged under the registry key “HKLM\Software\Microsoft\Windows NT\CurrentVersion\Svchost“. Every gathering gives diverse levels of get to; “netsvcs” is one of the majority astounding advantaged bunches for administrations with Windows XP system get to, plus in this way it will habitually utilized by aggressors. The “netsvcs” esteem is a string exhibit of administration names to be stacked in this gathering, as portrayed in the screenshot underneath.
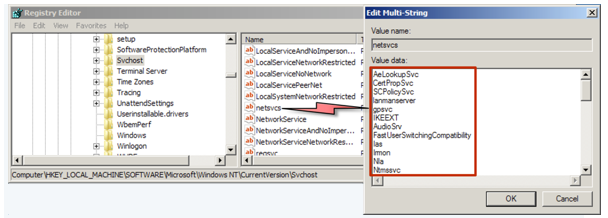
Attackers can manhandle facilitated administrations to stack a pernicious DLL in a few ways. One approach is to pick a facilitated benefit name that is “unused” – that is, for which there is no administration arranged under “HKLM\SYSTEM\CurrentControlSet\services“. Malware droppers could burn through these unused sections, make the essential registry keys, as well as in this way keep up constancy as a facilitated benefit. For instance, on more established adaptations of Windows, assailants regularly focused on the administration, which introduced “netsvcs” assemble yet frequently idle without a relating arrangement.
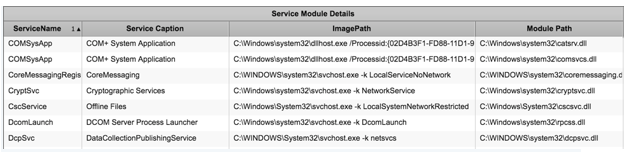
Identify Rogue Service DLLs
To identify Rogue service gives a few sensors that can help us effortlessly distinguish as well as examine benefit DLLs that will be large for business scale. In the first place, it will present another sensor, “Benefit Module Details” to be incorporated into the expected arrival of our Incident Response arrangement. This image beneath shows incomplete yield from this sensor.
Mitigation strategies
We will using mitigation strategies to protect our OS from any malware attack or incorporated which will allow us to easily detect the malware virus.
Host-Based Firewalls
Windows XP incorporate an inherent firewall that hinders every one of these ports in its default arrangement. To confirm that the implicit firewall is turned on plus obstructing these ports, go to the Network Connections control board, right-click every system association thus, select Properties, and afterward tap the Advanced tab.

Confirm that the check box under “Web Connection Firewall” is chosen. Not with standing when a framework is on a secured arrange, turning on the Internet Connection Firewall might be judicious on the grounds that, while the system might be shielded from untouchables, it is not shielded from insiders who have as of now been misused. If it’s not too much trouble take note of that numerous organizations, in any case, have arrangements which don’t allow utilization of Internet Connection Firewall inside the firewall since it pieces remote administration of those frameworks.
Then again, an equipment firewall can be utilized to secure a little system against assault. Such firewalls are moderately reasonable and are generally exceptionally easy to set up. It is accessible for buy in many hardware stores and at Microsoft’s online shop. It is dependably a judicious security measure to check that the ports are to be sure being obstructed in the wake of sending any host-based firewall measure. The port scanners recorded above can be utilized for this confirmation.
IPSec to Obstruct Attacks
When using Windows XP on QUT virtual machine, it is additionally conceivable to utilize IPSec to obstruct these ports. In any case, to be successful, a strategy would need to piece all the helpless ports totally, which will require security over these ports with hosts who cannot be trusted as well as known to be fixed. A bargain which trusts every OS in a space, require a lone solicitations security which comes out to be altogether viable solution. The reason is that such a strategy would permit contaminated machines that are mistakenly thought to be sheltered to impart unobstructed plus in this way assault the host that should be secured.
A basic IPSec arrangement is accessible. This arrangement hinders all activity over the helpless ports. To utilize this strategy, first download along with concentration for the record to a known area on windows xp network framework. Open Local Security Settings, right-click specify “IP Security Policies on Local Machine” specify “All Tasks” as well as select Import Policies.Then open the DCOMIPSEC strategy, which is one of the documents that were separated from the IPSecTools.exe file.
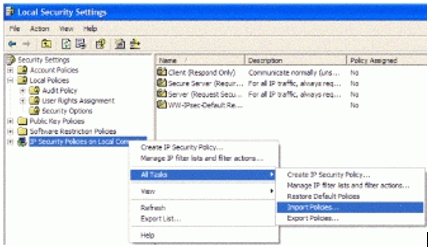
Since the strategy has been transported in, it must be allocated. Until an arrangement is allocated, it has no impact and to appoint the strategy, we have to right-tap the fancied approach then select “Relegate” The DCOM.IPSEC channel incorporates 2 strategies. One obstructs every DCOM movement aside from other CIS movement. Options will arrive which says not to utilize the approach that likewise pieces CIS activity on a framework that must serve HTTP movement as it will likewise square up HTTP as well as HTTPS activity.
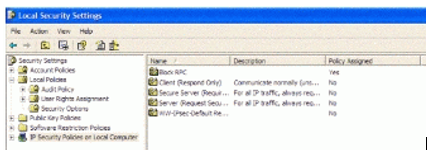
After finishing the above step, we will take note of that if there are some other arrangements are being relegated in the current scenario, they shall be unassigned by this activity. On the off chance, this Group Policy will determine an IP Security Policy, and other policies shall abrogate confidentially with doled out arrangements. In a domain, where these Policies are utilized to circulate Internet Protocol Security Policy, the DCOM arrangement shall be disseminated by means of Group Policy to every single influenced Window XP and higher PCs.
With the arrival of informational technology, computer system assignment help has started gaining importance in the education field. The information technology is related to computer and computing technology and today, it has become the backbone of the modern civilization. With almost every aspect of the society relying on the information technology, the demand of experienced professional has rapidly increased. There are several industries that are closely associated with the IT such as computer hardware, software, telecom equipment, electronic e-commerce, etc.
Along with studies student may have to write technical assignment on Windows XP, Oracle VM Virtual Box, application development and more. BookMyEssay provides guaranteed satisfaction with the commitment to deliver the quality assignment within the deadline. Being a leading academic writing service provider BookMyEssay has already worked on more than 3000 technical assignments around the world. Their service network is extended to countries like U.K, U.A.E, Australia, New Zealand, Malaysia and so many other countries. They are the right assignment partner for students.
Starting from under graduation to master students require technical homework help online to complete their technical writing tasks. Our online assignment writers have been assisting students all around the world with their technical assignment, case study writing, report writing, and technical thesis writing tasks. With the website scoring, good grades in the technical subject is not a dream anymore. Visit them to book your computer assignment today!


